Email Hosting
January 17, 2024
Statistics on email spam around the world
January 18, 2024
New phishing scheme found in svg files
Using HTML documents embedded in phishing emails is a standard technique used by cybercriminals. There is no need to include the link in the body of the email. HTML is often easily detected by anti-spam mechanisms and email antivirus programs.
It has been discovered that in addition to HTML, there are also attempts to use SVG files by inserting JavaScript and modifying them to be difficult to read (obfuscate) to avoid detection by security systems.
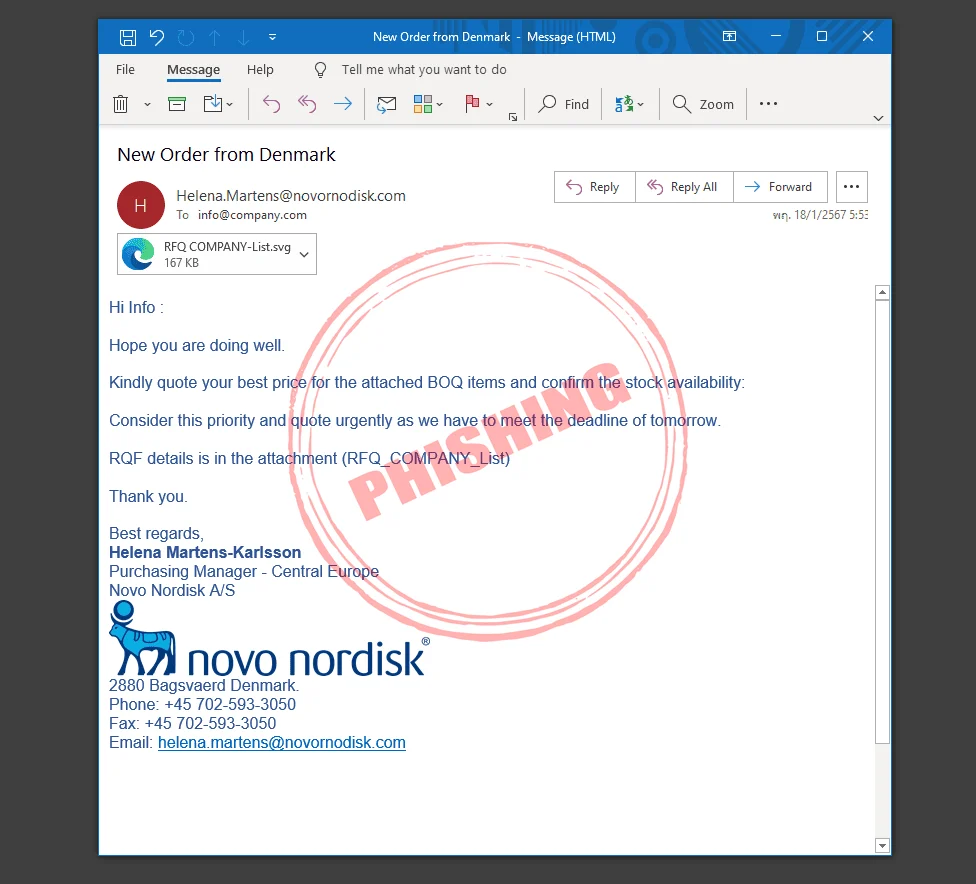
Email phishing format
Most often, the format and content of emails are notifications of order confirmations, payment notifications, product charges, or services, which may be offered using a relationship with an individual, financial institution, or a position such as CEO, company owner, or bank officer. So that email recipients are not suspicious and have trust, there may be mention of the urgency of the need to fill out or provide personal information, such as a username and password for logging in to an organization, or a username and password for conducting financial transactions such as E-Banking and other.
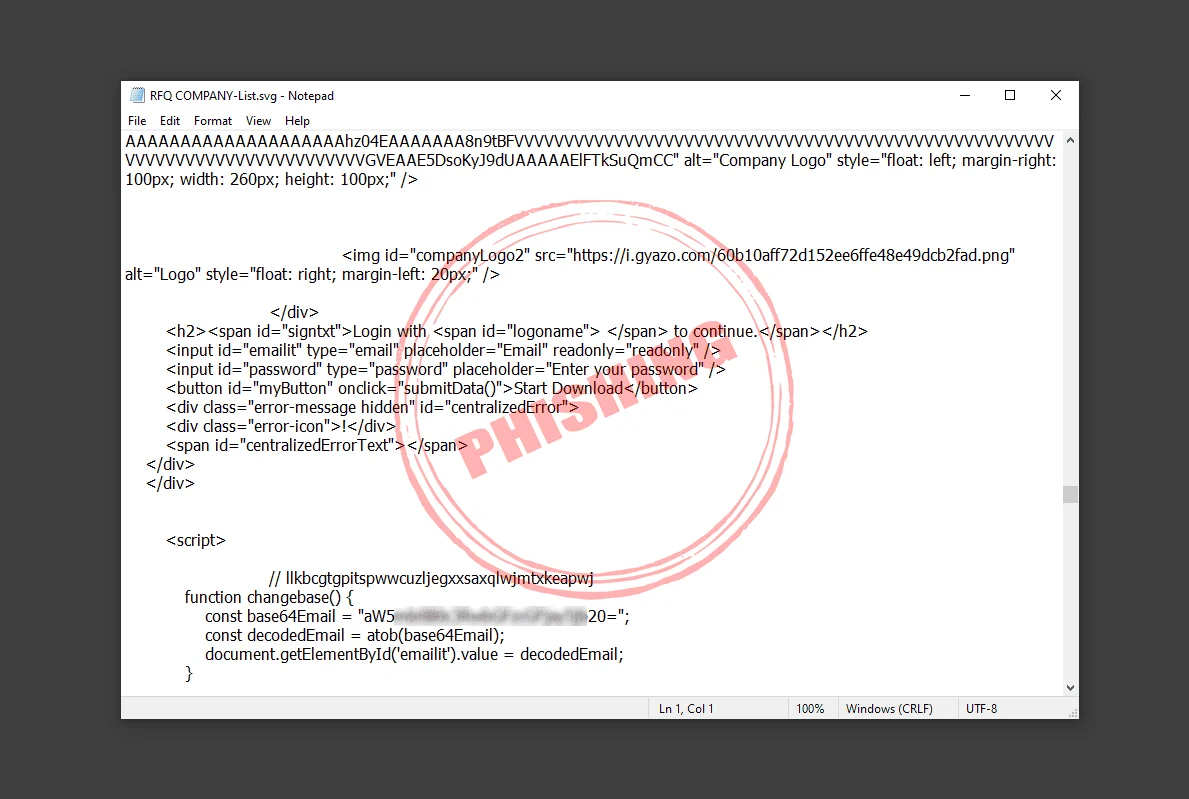
Although there were attempts to hide the formatting (obfuscate) of JavaScript or HTML, after investigating, it was found that the function of the said file is to create a form page for users to enter their email password. There will be a trick with the user that if they want to open and view the file or open and view the information sent with that email, users need to enter their password first. In this way, users lack knowledge or understanding and enter their password. The entered password will be sent to the creator of this system. Therefore, it is necessary to educate the users. If the requested system is found, enter any password. Make the user stop or close the window or program immediately and notify the system administrator immediately.
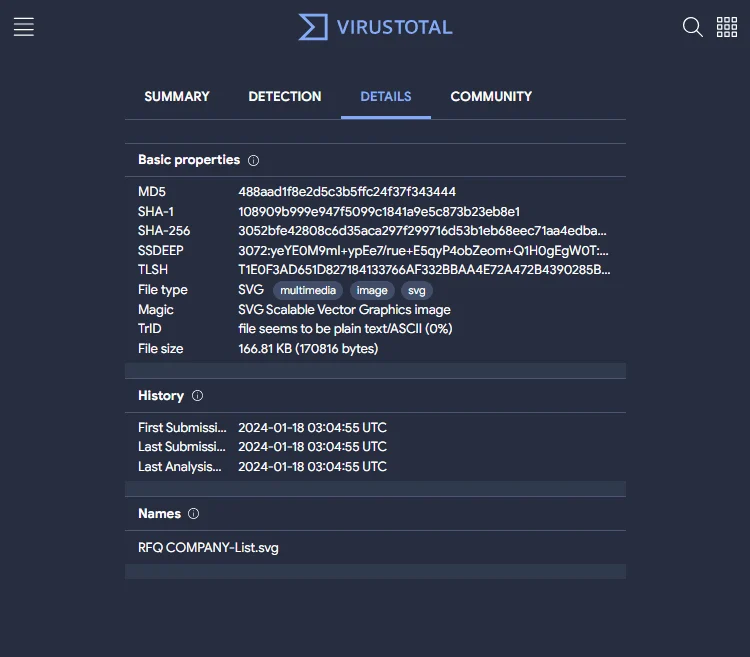
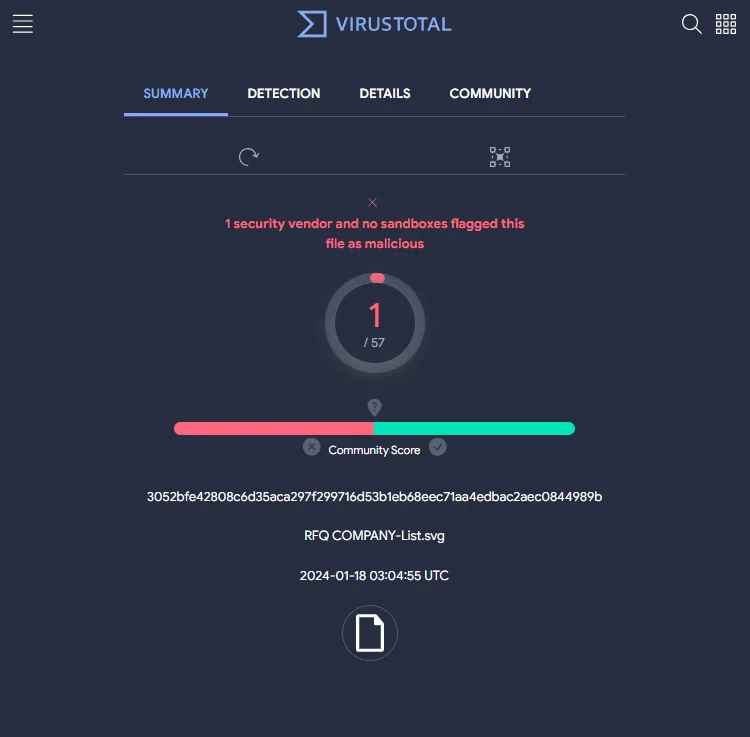
A review of VirusTotal's malware and file threat database found that only 1 out of 57 was detected at the time of the review.
VirusTotal is an antivirus company that was acquired by Google in 2012 and in early 2018 was moved under Chronicle, a new security company that is part of the Alphabet Group.
VirusTotal's service is a web-based service that allows users to upload files to check whether they are infected or not. At the same time, Google can also store information about infected files. To protect yourself and enhance the security of other services at all times, Uploader also has third-party software developed to make connecting to this service more convenient.
Protection from phishing
If you suspect that you may have been attacked by a phishing technique, there are steps you can take to prevent and deal with the situation:
1. Record as many details of the attack as possible, such as the date and time it occurred, especially any usernames, emails, or passwords you may have shared, and the location where the attack occurred, such as from an email or address. website
2. Change the password of the affected account or email immediately, including any other emails that may use the same password. As you change your password, it is a good idea to set a unique password for each account. You should also pay attention to the strength of the password you use.
3. If the attack affects your work or school email, notify the IT support staff at your work or school about the attack. If you share information about your credit card or bank account, you may need to contact the company and notify them of the fraud.
4. If you have lost money or are a victim of identity theft, the details in Step 1 will be helpful to local law enforcement agencies. Make a report to the agency as soon as possible.